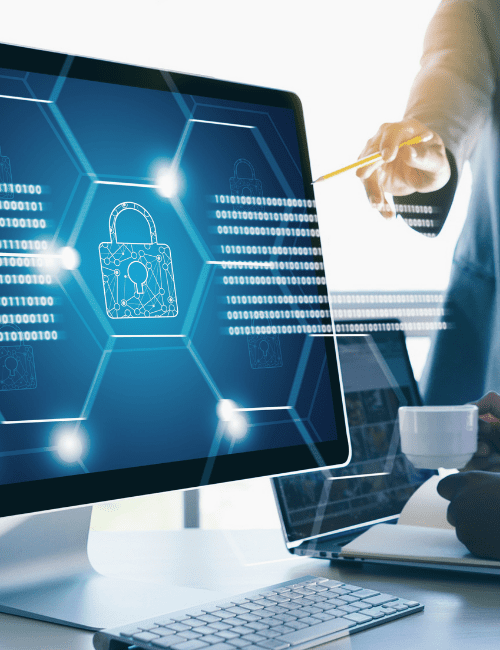
Defend your digital perimeter with comprehensive network security services. We identify vulnerabilities, test defenses, and secure your infrastructure to ensure continuous operations and safeguard your data.
A proven 4-step approach to identify, evaluate and mitigate risks that could impact your business.
We assess your environment and identify risks.
We evaluate threats, impact, and exposure.
We fix vulnerabilities and reduce risks.
We continuously track and improve security.
We provide advanced Network Security solutions that help businesses protect their digital infrastructure, sensitive data, applications, and communication systems from cyber threats and unauthorized access.
Our services include firewall configuration, threat detection and prevention, endpoint security, secure network architecture, vulnerability assessments, access control management, malware and ransomware protection, security monitoring, and incident response.
We work with organizations to build secure, scalable, and reliable network environments that reduce risks, improve compliance, and ensure uninterrupted business operations in an evolving cybersecurity landscape.

Regular vulnerability scanning is the first line of defense to continuously identify known weaknesses and misconfigurations across your network assets before attackers exploit them. Quickly find and fix common weaknesses within your network infrastructure before they become bigger problems. Our automated scanning solutions are designed to catch vulnerabilities early, saving you time and resources.
Automated Network Vulnerability Assessment: We conduct automated internal and external scans to pinpoint common network weaknesses, misconfigurations, and known vulnerabilities (e.g., outdated software, weak default passwords). Includes an initial scan and one post-remediation rescan to validate essential fixes.
While scans find known issues, penetration tests simulate real-world attacks, uncovering how vulnerabilities can be chained together or exploited with advanced techniques to breach your network. Simulate real-world attack scenarios to uncover complex, hidden flaws within your network, going beyond automated scans with advanced, human-driven testing.
Firewalls are your primary network gatekeepers. Misconfigured rules can create critical backdoors, making regular, expert reviews essential to maintain strong perimeter defense. Ensure your primary network defenses are optimized and free from critical misconfigurations that could expose your network.
Firewall Rule Review: We review your primary firewall rule sets against security best practices, identifying critical misconfigurations and potential security gaps that could expose your network.

High-level overview of network security, key risks, and strategic recommendations.

Prioritized action plan for focused vulnerability remediation based on severity and exploitability.


Follow-up expert support to clarify findings and assist during remediation.
ArmourIQ specializes in network vulnerability scanning, network penetration testing, and firewall rule reviews, delivering actionable security insights to defend your digital perimeter. Trust our network architecture security expertise to build and maintain your organization’s secure backbone against evolving cyber threats. Our expertise in network architecture security ensures your infrastructure is robustly protected against evolving threats, forming the secure backbone of your entire organization.
Our methodical process ensures a comprehensive evaluation of your network’s security posture, leading to actionable insights and enhanced resilience.

We collaborate with your team to map your network landscape, identify key assets, and align objectives ensuring our security assessment is precise and purpose-driven.

Through a blend of automated tools and expert-led analysis, we uncover hidden exposures, insecure configurations, and overlooked weaknesses across your network infrastructure.
You receive an impact-focused report that highlights critical threats first—equipping your team to act fast and fix what poses the greatest risk.
Our specialists guide you through each finding, delivering strategic advice and remediation planning that aligns with your operations and long-term security goals.
Network security is an ongoing journey. We recommend continuous monitoring and periodic assessments to adapt to new threats and evolving network infrastructure.
ArmourIQ’s network security approach is grounded in globally recognized frameworks such as NIST, ISO 27001, and SANS, with network penetration testing methodologies aligned to OSSTMM, PTES, and MITRE ATT&CK. Our assessments are tailored to help you meet compliance obligations across PCI DSS, HIPAA, GDPR, and other regulatory requirements—while enhancing your network’s real-world resilience.
We go beyond surface-level scans to deliver actionable insights, enabling you to identify, prioritize, and remediate threats across your digital perimeter with precision.
A vulnerability scan identifies known weaknesses in your network using automated tools. A penetration test goes a step further by simulating real-world attacks to validate how vulnerabilities can be exploited and assess the impact of potential breaches.
Yes. Depending on the engagement type, we can simulate internal threats, perform pivoting, and attempt lateral movement to test how an attacker might move through your environment.
No. We conduct all assessments in a non-disruptive manner.
We perform a manual review of firewall rule sets using a combination of custom scripts and vendor tools, benchmarking them against industry best practices and your business needs.
Yes. We offer remediation guidance sessions post-assessment to help your technical team understand and implement the required fixes effectively.
Yes. We include post-remediation rescans as part of our PT and VA services to verify that vulnerabilities have been successfully addressed.
Let’s work together to identify risks, close gaps, and build a stronger, more resilient security posture.
Copyright © Twinflare Technologies LLP, dba ArmourIQ 2025. All Rights Reserved.